Enterprise Device Management Platform
Complete centralized control over your thin client infrastructure — from device discovery and onboarding to remote management, patch deployment, and security compliance.

Complete centralized control over your thin client infrastructure — from device discovery and onboarding to remote management, patch deployment, and security compliance.

Enterprise-grade modules for managing, monitoring, and securing your entire endpoint fleet.
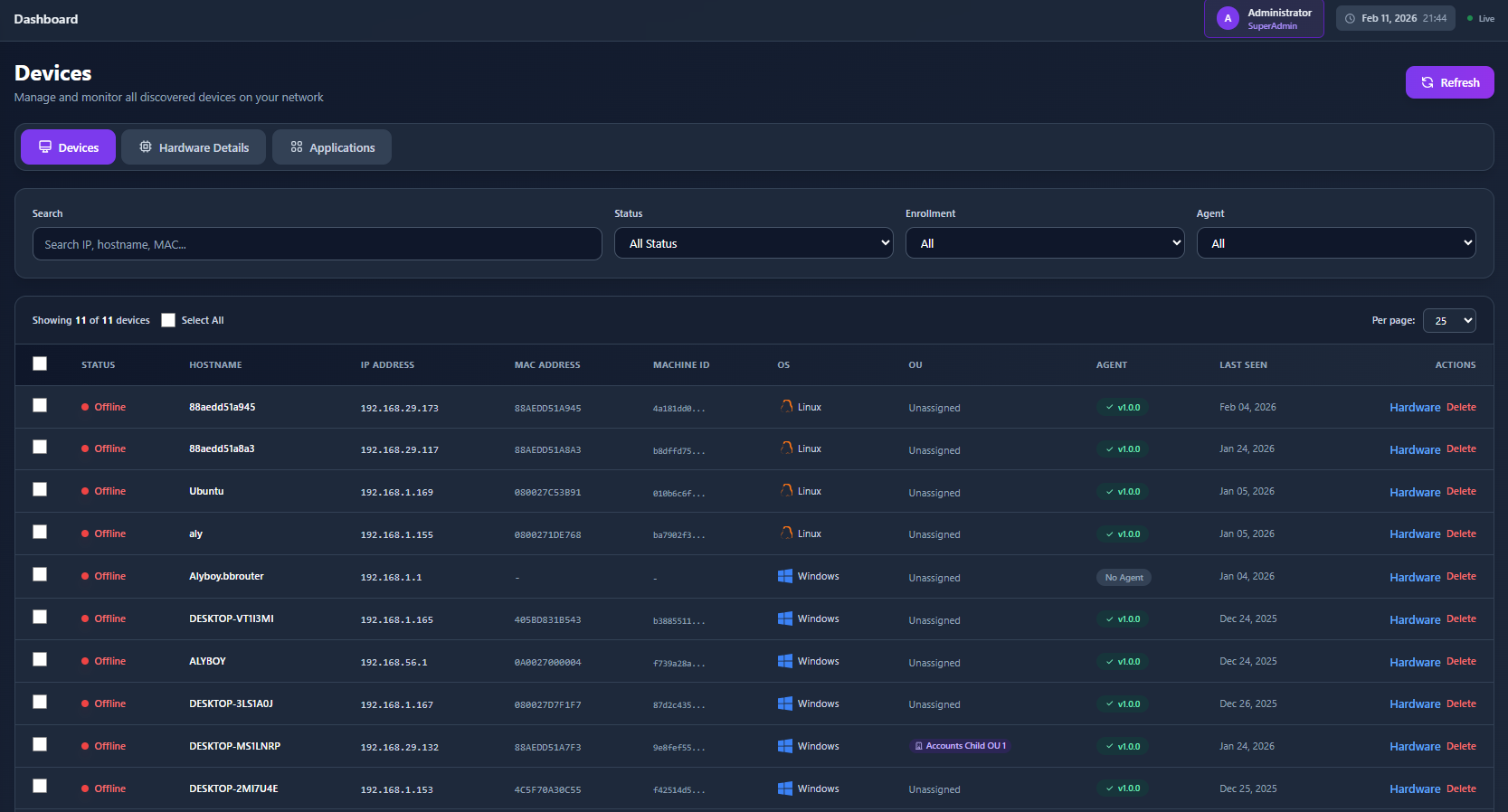
Automatic network discovery identifies all thin clients. Approval workflows ensure only authorized devices are managed, with automated agent deployment.
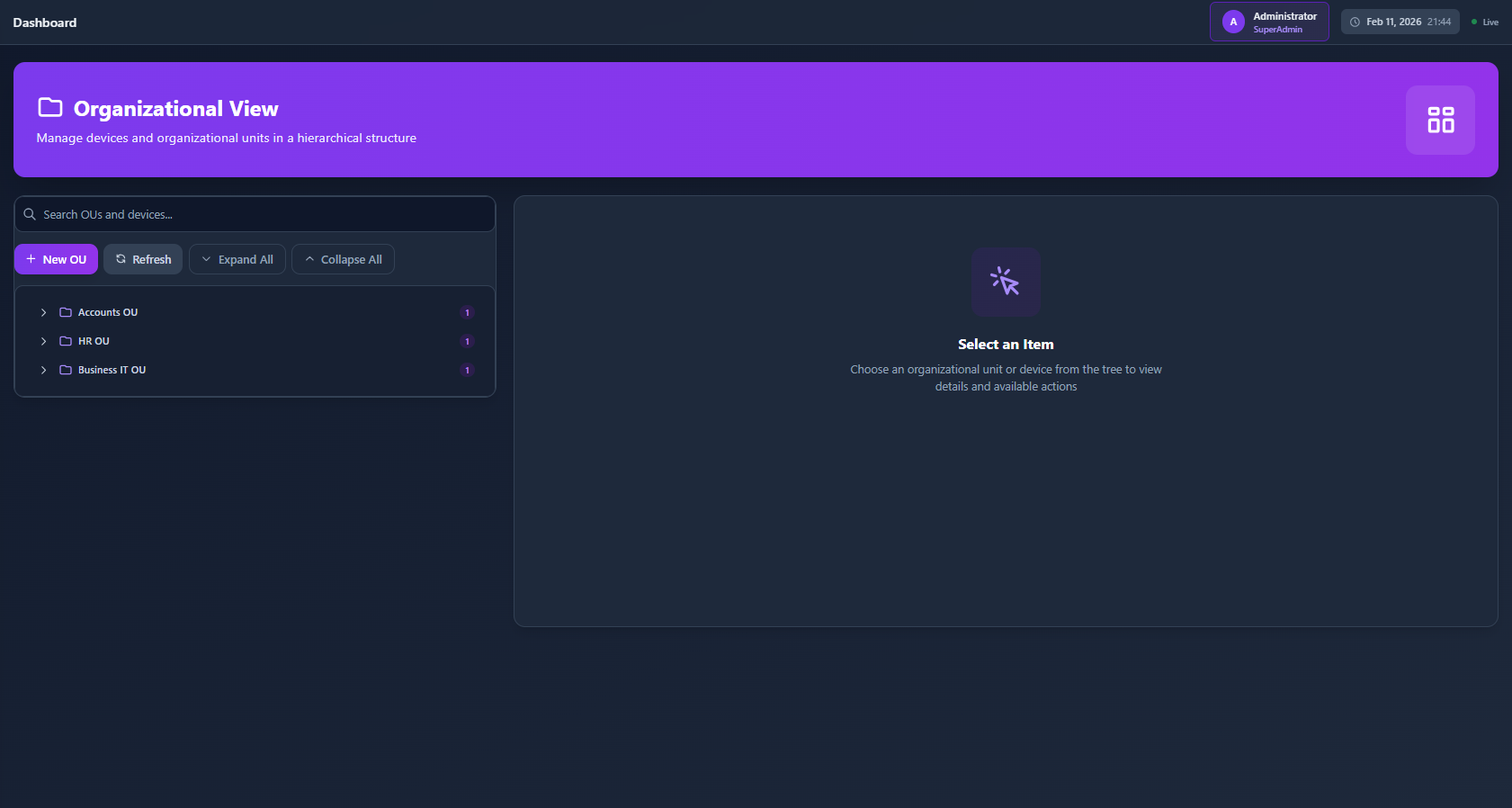
Organize devices into Organizational Units mirroring your company structure. Apply policies, configs, and patches to entire departments simultaneously.
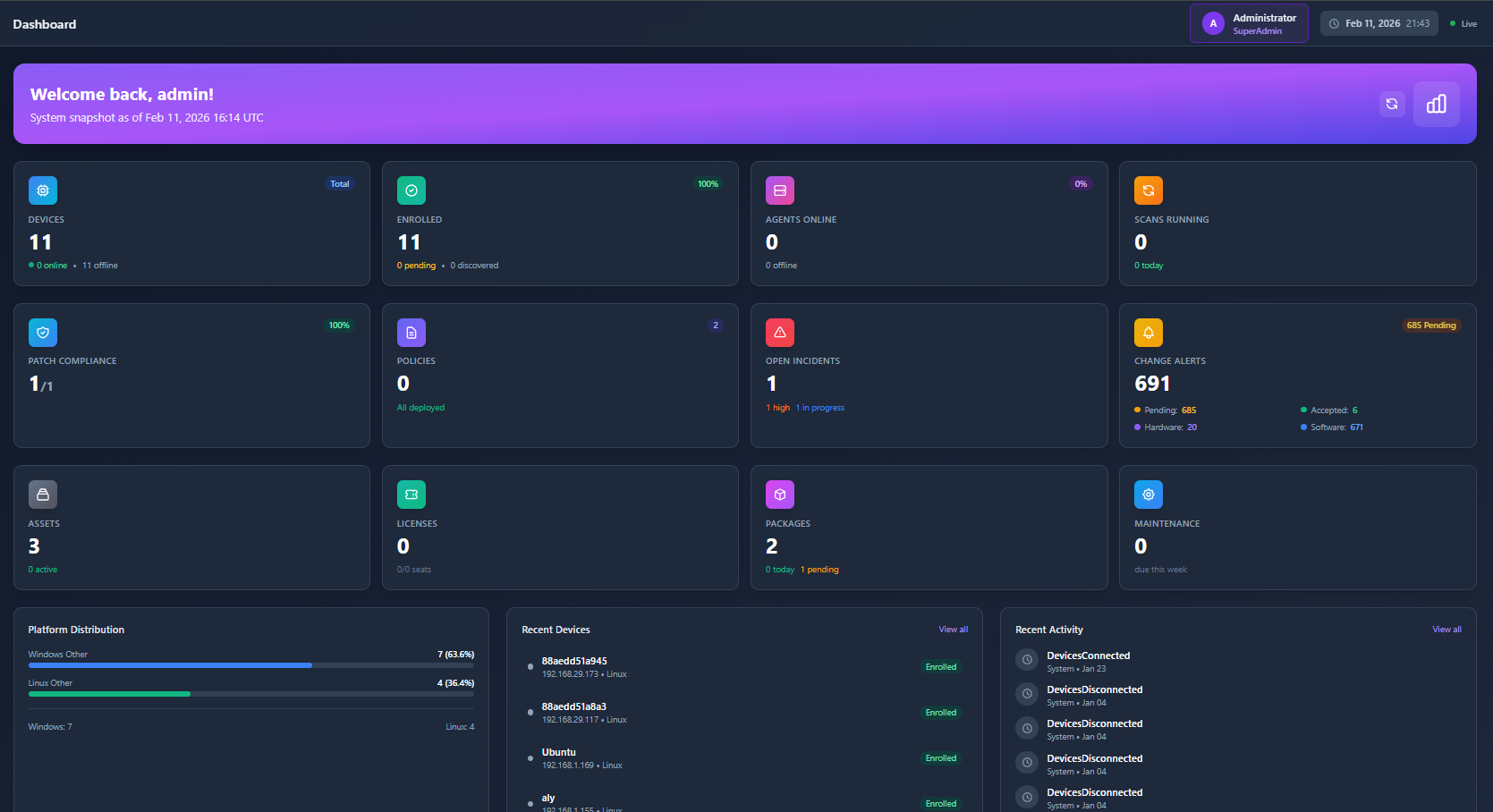
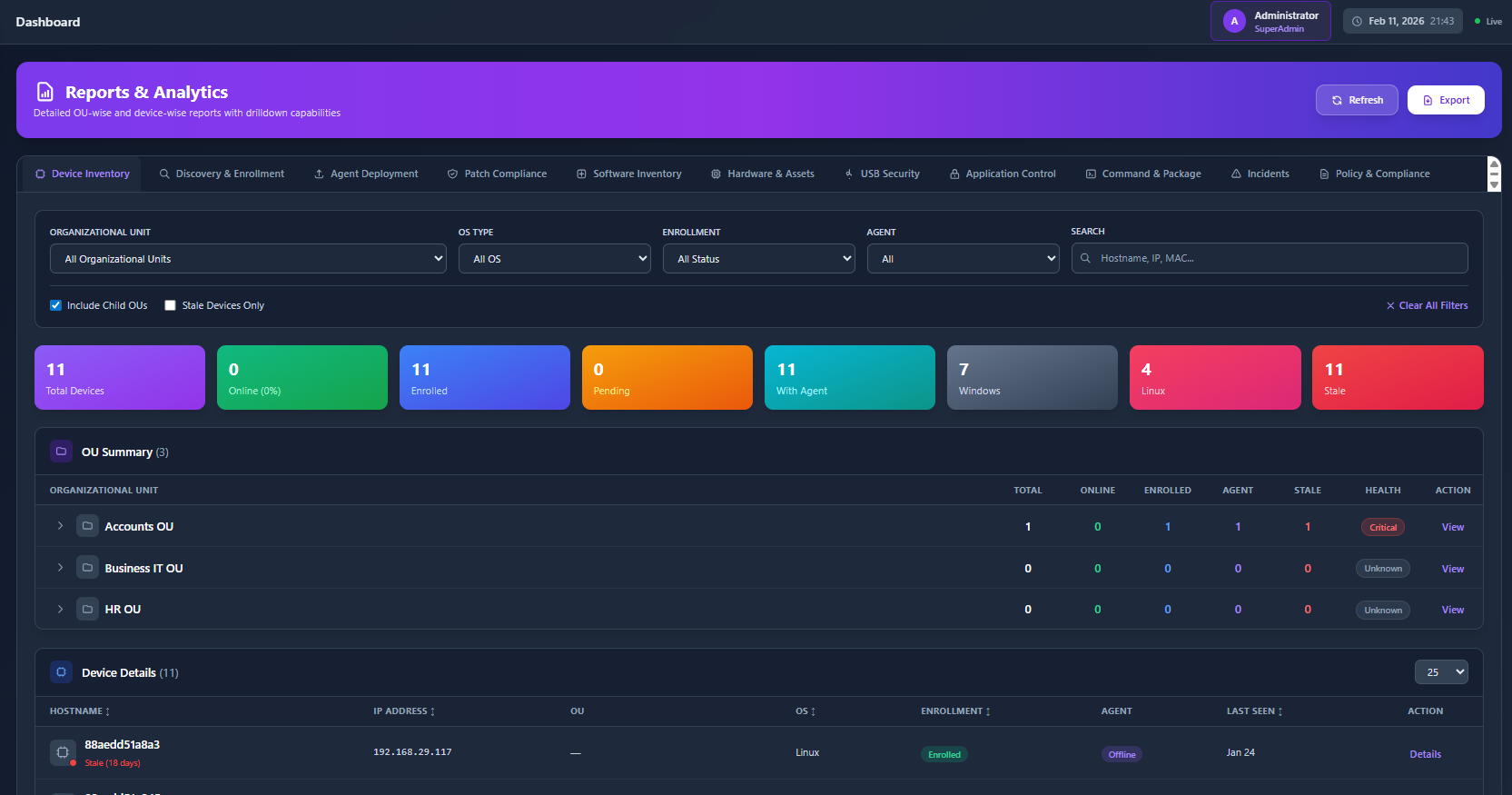
Detailed dashboards with real-time visibility into infrastructure health, performance metrics, security status, and device utilization trends.
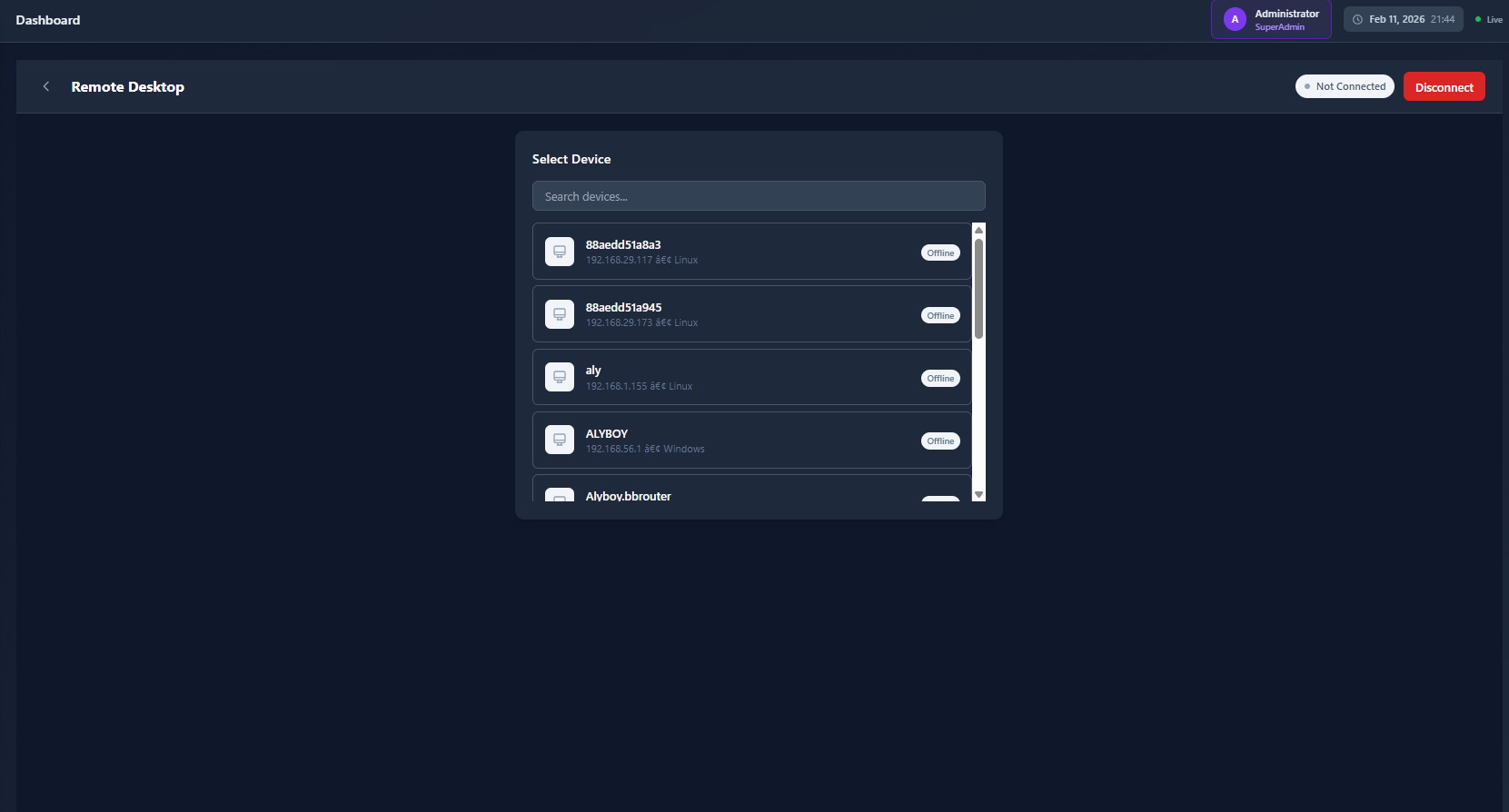
Built-in VNC and remote desktop for direct device access — troubleshoot, configure, or support users without physical site visits.
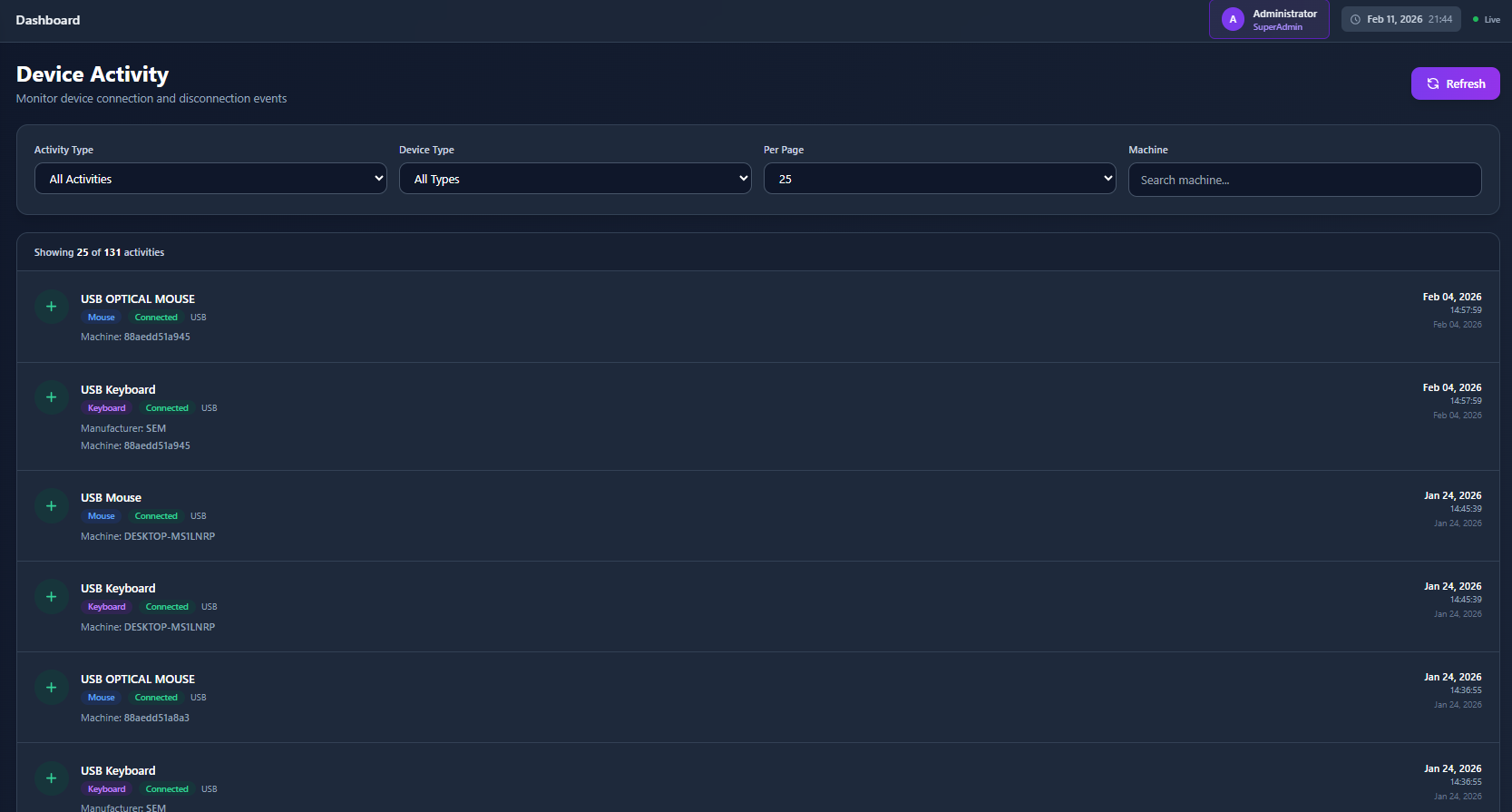
Centralized USB device policy control. Define permitted devices and vendors, block unauthorized peripherals while allowing approved hardware.
Deploy, update, and remove software centrally. Push applications to individual devices, groups, or entire OUs with version control.
Run scripts and commands remotely across managed devices. Automate routine tasks and respond rapidly to security incidents or operational needs.
Automated security patch deployment with scheduling, pilot group testing, and verification. Priority deployment for critical vulnerabilities.
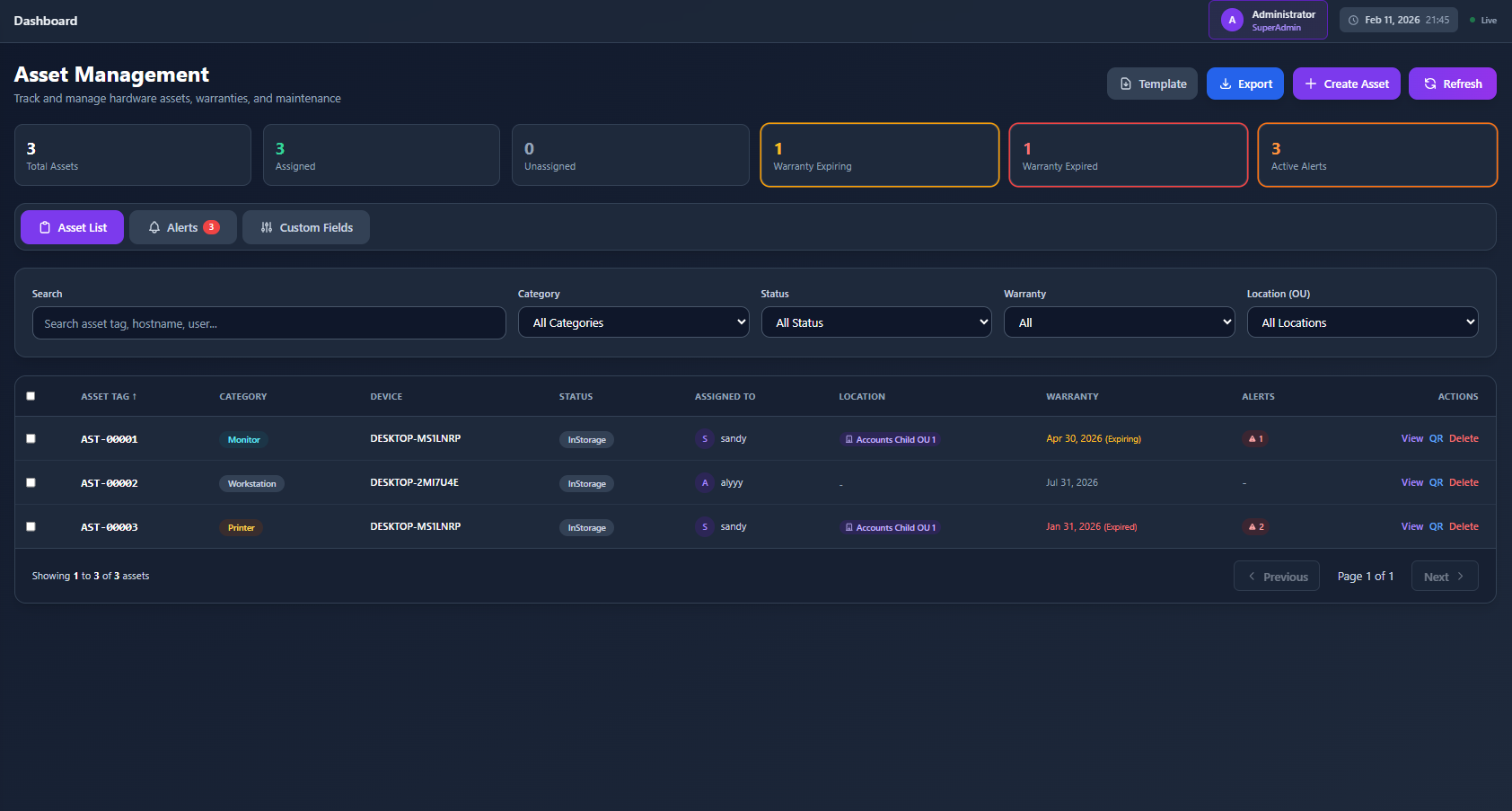
Complete hardware and software inventory — device specs, installed apps, peripherals, and component details automatically cataloged and tracked.
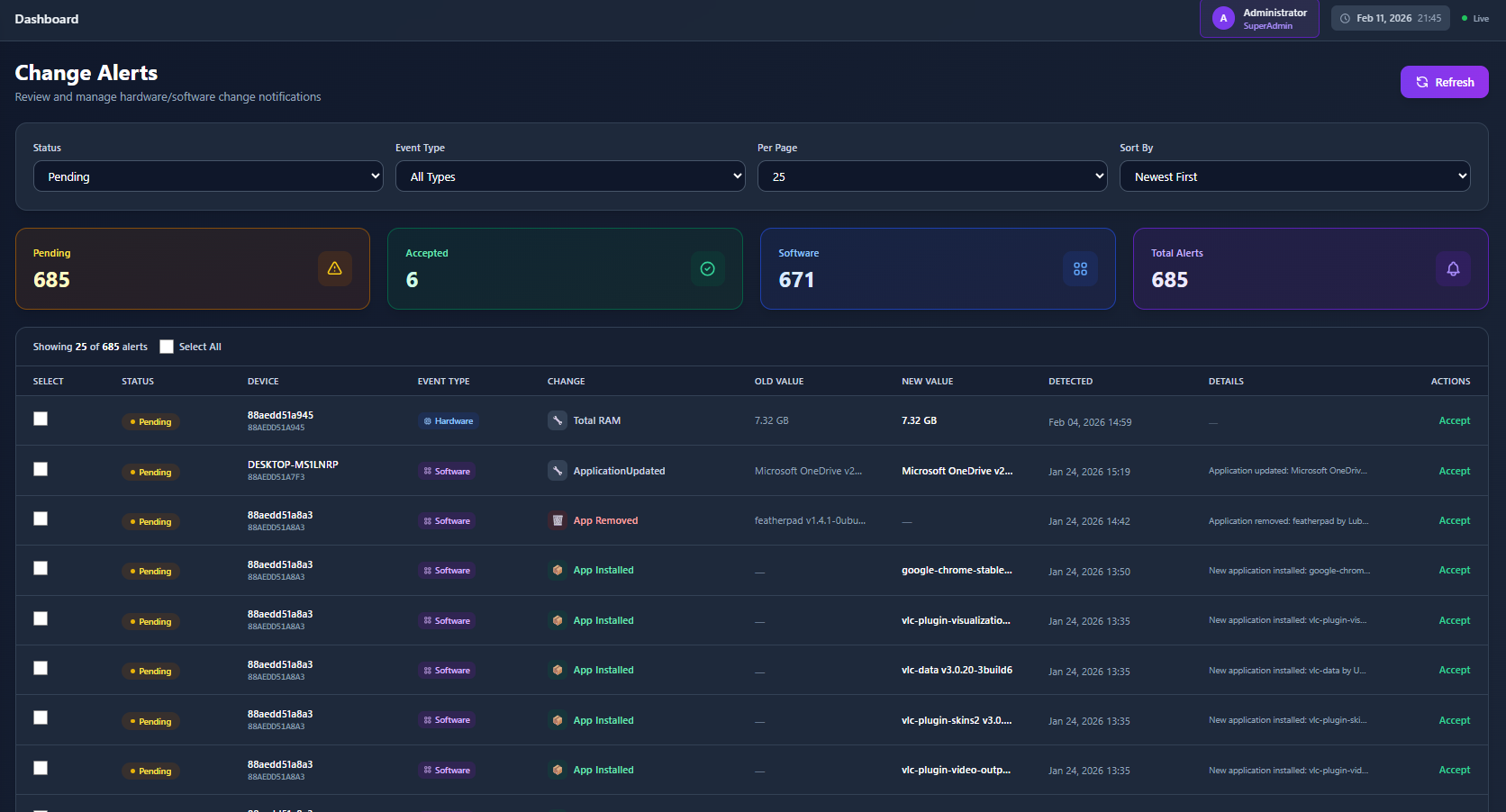
Granular audit trails capturing hardware changes, USB events, user logins, application usage, and system modifications for compliance and investigations.
Protect your infrastructure with role-based access, audit trails, and incident management.
Restrict administrative functions based on user roles. Principle of least privilege prevents unauthorized access and reduces misconfiguration risks.
Integrates with existing identity systems for centralized control over DMS access, permissions, and administrative actions.
Track, prioritize, and resolve issues systematically. Auto-created tickets from alerts with response time tracking and recurring issue identification.
Screenshots of the CMS interface — click any image to expand.
Get in touch to learn more about our Centralized Management System or to discuss custom requirements for your infrastructure.